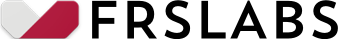
International Revenue Share Fraud (IRSF Fraud) has been a bane for communication service providers for over a decade. IRSF perpetrators make vicious attacks, often taking the operators by surprise, and in some cases, leaving smaller operators at the brink of closure.
The GSMA provides a comprehensive definition of what IRS Fraud is: “International Revenue Share Fraud is a form of fraud whereby the perpetrator artificially inflates traffic by generating calls to certain portions of international number ranges with no intention to pay for the calls (or paying where there exists some form of arbitrage opportunity), or by stimulating calls by others to the number ranges. The fraudster receives a share of the revenue from termination charges obtained by the number range holder for inbound traffic to the number ranges.”
The modus operandi for fraudsters includes:
- Acquiring SIM cards illegally.
- Hijacking SIM cards from unsuspecting customers.
- Using SIM cards from stolen phones.
- Obtaining SIM cards through subscription fraud.
- Hacking into PBX systems or hijacking number ranges.
- Installing malware on devices that generates calls discreetly.
Once fraudsters obtain SIM cards or compromise PBX systems, they often select International Revenue Share (IRS) destinations in collaboration with IPRN providers and content providers that offer lucrative payouts to generate traffic. To maximize their revenues, fraudsters employ various techniques such as international call forwarding, malware, and deploying multiple moles simultaneously to drive traffic.
Many IRSF numbers are regular numbers advertised as premium rate numbers. There are no centralized premium rated number that you can readily use for blocking or analysing before allowing the call to proceed. So, having a bunch of rules in your FMS is not going to cut it.
Frequently, these calls continue until the number range owner or the operator detects the attack and blocks access. Typically, fraudsters then move on to another number or destination to continue their attack until the SIM cards are blocked by the originating home operator. In many cases, the originating operator may struggle to recover money from the perpetrators.
Each operator routes the calls based on a convoluted algorithm and routing agreements. Therefore, it would be futile to go down the rabbit hole to identify the perpetrators of IRSF or Wangiri fraud.
Having worked with a number of operators, both large and small, it becomes apparent that no one is immune to IRSF attacks. This fact is further supported by the wide range of IRSF destinations, which spans over 220 countries, covering virtually every nation on the planet. Even if one number is blocked, fraudsters have thousands of other numbers and destinations to choose from.
Agreements are often out of reach of investigators, so even if you have a mandate, you will keep wondering why you couldn’t figure out that you couldn’t figure out. Fraudulent operators are lean and efficient over regular operators. They use numerous techniques to terminate, mis-route such that investigations are impossible as only a small proportion is re-routed.
The cross-border nature of IRSF also poses significant challenges for law enforcement agencies attempting to track down the perpetrators. For instance, the complex IRSF cycle begins when SIM cards are acquired by Mr. X, a national of Country A, who then ships the SIM cards to Mr. Y, a national of Country B, residing in Country C. Subsequently, calls are placed to Country D, and these calls are rerouted to an IRS or PRS number located in Country E, owned by a company registered in Country F, with money being channeled through multiple bank accounts. This intricate web of international connections makes it an exceptionally formidable task for law enforcement teams.
Numbers are often hijacked for short periods to test and arrangements made to defraud – usually between 4 and 48 hours. If you are using a number database for prevention, you better make sure that it is a real time.
Having strong primary fraud controls such as Application Fraud Prevention and Subscription Fraud Detection are indeed a must. On top of this, operators will need more than just a fraud management system to detect and prevent IRSF attacks. For instance, numbers called in IRSF incidents are usually not part of official national numbering plans, so the originating operator cannot easily identify the B-numbers as premium rate service numbers and add them in the fraud management system to generate alerts.
The IRSF fraud schemes are ever growing from fraudulent SIMs, hacking computers and communication systems to malware that automatically dials while you are still swiping your screen, RCS messages that are virtually undetected and delivered to your inbox as real (apart from wiping out your savings, you also get charged a premium for returning the call that purportedly came from the post office announcing of a missed parcel delivery – pretty painful!).
Recognizing the unique methods employed in IRSF fraud, we have developed a novel IRSF database called Rombus, which contains pretty much all of the test numbers advertised by IPRN providers. Utilized as a hotlist, this database could prove to be a valuable weapon in the battle against IRSF fraud.
If you would like to learn more about our IRSF fraud prevention solution, please get in touch.
About
We are your friends at frslabs
FRSLABS is an award-winning research and development company specialising in customer onboarding, identity verification and fraud prevention solutions for businesses. Whether you are a big bank, insurance, telco or a small investment broker, we help you onboard and verify your customers with greater flexibility, compliance and reliability.
Built for you, not for investors
We do what is right for you (and only you) at scale. Nothing is off-limits for us when it comes to innovation, a culture best reflected in the array of patents we have filed. We want to be your trusted partner, to build the solutions you need, and to succeed when you succeed.
Priced for success
We are driven by our mission to touch a billion lives with our tools and not beholden by venture capital or mindless competition. We therefore have the freedom to do the right thing, and price our products sensibly, keeping your success and our staff in mind.
Supported by humans
Whatever it takes, we are here to help you succeed with our products and services. For a start, you get to talk to a human for help, not bots, to figure things out one-to-one. Whatever your needs, however trivial or complex it may seem, we have you covered.
**